23.10.2020
pcdx
video
As the novel coronavirus (COVID-19) continues to spread, many businesses are assessing how they can prioritize their employee safety and still maintain regular business operations.
One solution many businesses are turning to is recommending employees to work from home to avoid potential illnesses. To help ease the burden on businesses, Microsoft, Google, LogMeIn, Cisco Webex, and Zoom are providing free remote working tools.
With the likely increase in remote work, companies will have to prepare in various ways to avoid cybersecurity risks or interruptions to business. “When supporting a remote workforce, understand that security controls shift. Therefore, firewalls, DNS, and IDS/IPS could be ineffective when employees head home. Most environments that support VPNs should be able to protect the remote user, be sure to account for the bandwidth of users and remote desktop sessions,” said Dan Garcia, Senior Information Security Engineer II at Datto.
CISA’s VPN Guidance
The Cybersecurity and Infrastructure Security Agency (CISA) released an alert to encourage organizations to adopt a heightened state of cybersecurity. According to the CISA, remote work options require a VPN solution to connect employees to an organization’s network. The CISA encourages organizations to review the following recommendations when considering alternate workplace options:
• Update VPNs, network infrastructure devices, and devices being used to remote into work environments with the latest software patches and security configurations. See
CISA Tips Understanding Patches and Securing Network Infrastructure Devices.
• Alert employees to an expected increase in phishing attempts. See CISA Tip Avoiding Social Engineering and Phishing Attacks.
• Ensure IT security personnel are prepared to ramp up the following remote access cybersecurity tasks: log review, attack detection, and incident response and recovery. Per the National Institute of Standards and Technology (NIST) Special Publication 800-46 v.2, Guide to Enterprise Telework, Remote Access, and Bring Your Own Device (BYOD) Security, these tasks should be documented in the configuration management policy.
• Implement MFA on all VPN connections to increase security. If MFA is not implemented, require teleworkers to use strong passwords. (See CISA Tips Choosing and Protecting Passwords and Supplementing Passwords for more information.)
• Ensure IT security personnel test VPN limitations to prepare for mass usage and, if possible, implement modifications—such as rate limiting—to prioritize users that will require higher bandwidths.
• Contact CISA to report incidents, phishing, malware, and other cybersecurity concerns.
The CDC has released some best practices for a disease outbreak plan:
• Review human resources policies to make sure that policies and practices are consistent with public health recommendations and are consistent with existing state and federal workplace laws (for more information on employer responsibilities, visit the Department of Labor’s external icon and the Equal Employment Opportunity Commission’s external icon websites).
• Explore whether you can establish policies and practices, such as flexible worksites (e.g., telecommuting) and flexible work hours (e.g., staggered shifts), to increase the physical distance among employees and between employees and others if state and local health authorities recommend the use of social distancing strategies. For employees who are able to telework, supervisors should encourage employees to telework instead of coming into the workplace until symptoms are completely resolved. Ensure that you have the information technology and infrastructure needed to support multiple employees who may be able to work from home.
In addition, managed service providers (MSPs) are recommending the following best practices and advice for how businesses can remain secure through potential remote work scenarios.
• Use a Secure WiFi Network: If possible, you should work on your secure, private home network instead of relying on public WiFi. If you send your data through an unsecured WiFi connection, you lose the power of privacy making it possible for cybercriminals to intercept your data. You may be putting personal information at risk if you are accessing your email account or sending sensitive data over a public WiFi network. It’s essential to ensure your network is secure through the use of a VPN and a strong password that isn’t easily cracked.
• Secure Your Home Workstation: Ensure you have fully patched and updated anti-virus and anti-malware software. It’s important to follow the same best practices you would as if you were in the office, and report any suspicious activity or concerns to internal IT or your MSP.
• Coordinate With Your Internal IT or MSP: When working remotely, it’s crucial to continue your typical cybersecurity best practices and reach out with any questions or concerns.
30.03.2020
George McCracken
standart
SentinelOneOne way or another, passwords are always in the news. They’re either being stolen in data breaches, or mocked for being too simple; derided as pointless, or lamented for being technologically backward. No matter what opinion any of us have on passwords, though, one thing is indisputable: we’re going to be using them today, tomorrow and for the forseeable future. Unlike touch or facial recognition technologies, passwords are used everywhere because they’re cheap to implement and simple to use. For end users, they are as low-tech as security tech ever gets. Of course, that ubiquity and simplicity is precisely what makes passwords attractive to thieves. In this post, we take a look at how hackers steal our passwords and what we can do to stop them.
1. Credential Stuffing
Risk Level: High
It is estimated that tens of millions of accounts are tested daily by hackers using credential stuffing.What Is It?
Credential stuffing, also known as list cleaning and breach replay, is a means of testing databases or lists of stolen credentials – i.e., passwords and user names – against multiple accounts to see if there’s a match.How Does It Work?
Sites with poor security are breached on a regular basis, and thieves actively target dumping user credentials from such sites so that they can sell them on the dark net or underground forums. As many users will use the same password across different sites, criminals have a statistically good chance of finding that userjanedoe@somesite.net has used the same password on janedoe@anothersite.com. Tools to automate the testing of a list of stolen credentials across multiple sites allow hackers to quickly breach new accounts even on sites that practice good security and password hygiene.
How Can You Stay Safe?
The key to not becoming a victim of credential stuffing is simple: every password for every site should be unique. Of course, that won’t prevent your password being stolen for one account on a site with poor security, but it does mean that any one compromise of your credentials will not affect you anywhere else on the internet. If you’re gasping at the thought of creating and remembering unique passwords for every site you use, see our Tips section near the end of the post.2. Phishing
Risk Level: High
Over 70% of all cybercrimes begin with a phishing or spear-phishing attack. Hackers love to use phishing techniques to steal user credentials, either for their own use, or more commonly to sell to criminals on the dark net.What Is It?
Phishing is a social engineering trick which attempts to trick users into supplying their credentials to what they believe is a genuine request from a legitimate site or vendor.How Does It Work?
Typically, but not always, phishing occurs through emails that either contain fraudulent links to cloned websites or a malicious attachment. Somewhere along the chain of events that begins with the user taking the bait, the fraudsters will present a fake login form to steal the user’s login name and password. Fraudsters will also use some form of interception between a user and a genuine sign-in page, such as a man-in-the-middle attack to steal credentials.How Can You Stay Safe?
Use 2-factor or multi-factor authentication. Although researchers have developed tricks to overcome these, in the wild cases are yet to be reported. Caution is your number one defense against phishing. Ignore requests to sign in to services from email links, and always go directly to the vendor’s site in your browser. Check emails that contain attachments carefully. The majority of phishing emails contain misspellings or other errors that are not difficult to find if you take a moment to inspect the message carefully.3. Password Spraying
Risk Level: High
It’s been estimated that perhaps 16% of attacks on passwords come from password spraying attacks.What Is It?
Password spraying is a technique that attempts to use a list of commonly used passwords against a user account name, such as123456, password123, 1qaz2wsx, letmein, batman and others.
How Does It Work?
Somewhat like credential stuffing, the basic idea behind password spraying it to take a list of user accounts and test them against a list of passwords. The difference is that with credential stuffing, the passwords are all known passwords for particular users. Password spraying is more blunt. The fraudster has a list of usernames, but no idea of the actual password. Instead, each username is tested against a list of the most commonly used passwords. This may be the top 5, 10 or 100, depending on how much time and resources the attacker has. Most sites will detect repeated password attempts from the same IP, so the attacker needs to use multiple IPs to extend the number of passwords they can try before being detected.How Can You Stay Safe?
Ensure your password is not in the list of top 100 most commonly used passwords.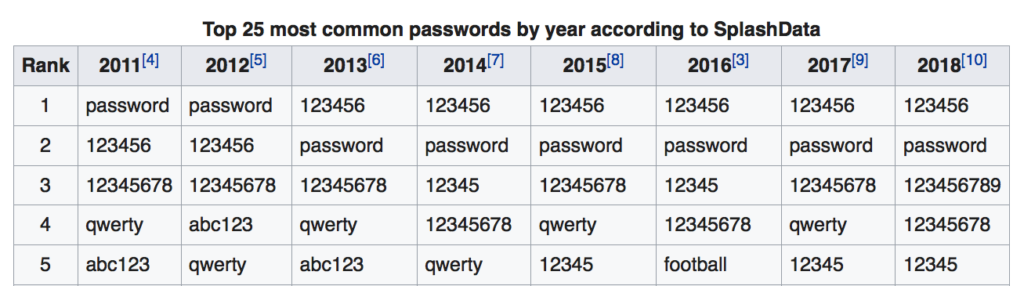
4. Keylogging
Risk Level: Medium
Keylogging is often a technique used in targeted attacks, in which the hacker either knows the victim (spouse, colleague, relative) or is particularly interested in the victim (corporate or nation state espionage).What Is It?
Keyloggers record the strokes you type on the keyboard and can be a particularly effective means of obtaining credentials for things like online bank accounts, crypto wallets and other logins with secure forms.How Does It Work?
Keylogging is more difficult to pull off than Credential Stuffing, Phishing and Password Spraying because it first requires access to, or compromise of, the victim’s machine with keylogging malware. That said, there are lots of publicly available post-exploitation kits that offer attackers off-the-shelf keyloggers, as well as commercial spyware tools supposedly for parental or employee monitoring.How Can You Stay Safe?
You need to be running a good security solution that can detect keylogging infections and activity. This is one of the few kinds of password theft techniques where the strength or uniqueness of your password really makes no difference. What counts is how well your endpoint is secured against infection, and whether your security software can also detect malicious activity if the malware finds a way past its protection features.5. Brute Force
Risk Level: Low
Surprisingly not as prevalent as people tend to think, brute forcing passwords is difficult, time-consuming and expensive for criminals.What Is It?
It’s the kind of thing that security researchers like to write about, or which you might see in TV shows: a hacker runs an algorithm against an encrypted password and in 3…2…1… the algorithm cracks the password and reveals it in plain text.How Does It Work?
There are plenty of tools like “Aircrack-ng”, “John The Ripper”, and “DaveGrohl” that attempt to brute force passwords. There’s generally two kinds of cracking available. The first is some form of “dictionary” attack – so called because the attacker just tries every word in the dictionary as the password. Programs like those mentioned above can run through and test an entire dictionary in a matter of seconds. The other type of technique is used when the hacker has (through means of a data breach) acquired the hash of the plain-text password. Since these can’t be reversed, the aim is to hash as many plain-text passwords as possible and try to find a match. Rainbow tables exist which list the hashes of common passphrases to speed up this process. One of the reasons why password cracking is not as viable a technique as some of the others we’ve mentioned is that encrypted passwords typically use a salt. This is some random data used in the encryption process that ensures no two plain-text passwords will produce the same hash. However, mistakes made by site administrators when using or storing salts and passwords can make it possible for some encrypted passwords to be cracked.How Can You Stay Safe?
The key to staying safe from brute force attacks is to ensure you use passwords of sufficient length. Anything 16 characters or over should be sufficient given current technology, but ideally future-proof yourself by using a passphrase that is as long as the maximum allowed by the service that you’re signing up to. Avoid using any service that doesn’t let you create a password longer than 8 or 10 characters. Worried about how you’d remember a super long password? See the Tips section below.6. Local Discovery
Risk Level: Low
Mostly a technique that would only be used in a targeted attack, either by a known acquaintance, relative, colleague or law enforcement.What Is It?
Local discovery occurs when you write down or use your password somewhere where it can be seen in plain text. The attacker finds the password and uses it, often without your knowledge that the password has been leaked.How Does It Work?
You’ve seen those movies where the cops go through the bad guy’s trash for clues as to what he’s been up to? Yep, dumpster diving is one valid way of gaining a password through local discovery. Do you have a Post-It note on the monitor, or a diary in the desk drawer with your Paypal credentials? There are more covert means of local discovery though, including sniffing bluetooth communicationsor finding plain text passwords in logs or urls. Shoulder-surfing is not unknown, too. That can be anything from a colleague surreptitiously hanging around behind your desk when you login, to CCTV in coffee shops and other public areas that could capture video of users as they type their login credentials into a website on their laptops.How Can You Stay Safe?
There’s no need to be paranoid, but do exercise the proper amount of caution. While the risk is low in general, if you make yourself the low-hanging fruit by leaving easily discoverable records of your password lying around, don’t be surprised if someone takes advantage of that.7. Extortion
Risk Level: Low
Probably lowest on the risk scale, but not unheard of.What Is It?
Somebody demands you give them your credentials. No subtefuge involved. The deal is you give up your password or they do something you won’t like.How Does It Work?
Straightforward blackmail technique that depends on the nature of the relationship between the attacker and the target. Someone may demand your password if they have the means to harm or embarrass you if you don’t comply, such as revealing sensitive information, images or videos about you, or threatening the physical safety of yourself or your loved ones. RAT malware that lets hackers spy on you through a web or video cam can expose you to this kind of extortion.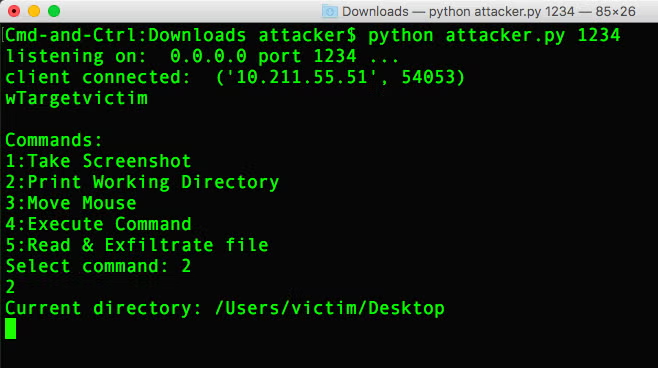
How Can You Stay Safe?
As ransomware victims are finding out on an almost daily basis, there’s no rule book for how to deal with extortion demands. It’s a trade off between the value of what they want versus the value of the harm they could do. Be aware that in some jurisdictions and in certain circumstances, giving in to an extortion demand could make you liable to prosecution under the law.Do Passwords Matter?
Some think not, but yes they do. Strong passwords will protect your from techniques like password spraying and brute force attacks, while unique passwords will protect your from credential stuffing, ensuring that the damage caused by a leak on one site will not negatively impact you elsewhere.Tips For Creating Strong, Unique Passwords
One of the main reasons why Credential Stuffing and Password Spraying are so successful is because people don’t like creating and remembering complex passwords. The good news – which really shouldn’t be news as it’s been true for quite some time – is that password managers will save you the effort. These are readily available and some browsers even have password suggestions built in. Of course, it’s true that these are not foolproof. They typically rely on a master password that, if compromised, exposes all the eggs in your single basket. However, the chances of being a victim of password theft if you use a password manager are significantly lower compared to if you don’t. We suggest the benefits of password managers hugely outweigh the risks, and we highly recommend them as a basic Security 101 practice.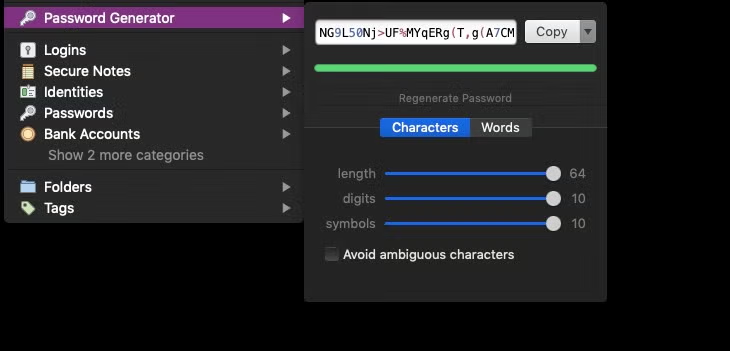
Conclusion
Passwords aren’t going away any time soon, and there’s even good arguments to suggest that they shouldn’t. While biometric data, facial and fingerprint scanning all have a role in helping secure access to services, the one over-riding beauty of a password is it’s the “something you know” and not the “something you have”. The latter can be taken away from you, in some cases legally, but the former cannot, so long as you ensure that it’s sufficiently complex, unique and secret. Combine that with two-factor or multi-factor authentication and your chances of suffering data loss through password hacking are both extremely low and – importantly – highly limited. If an insecure site does leak your credentials, you can be confident that it won’t affect you beyond that particular service.
28.08.2019
George McCracken
standart